So, we have set up previously OMS to act as our Log Correlation Engine. We receive alerts depending on events and all works well. The only downside is that the retention period for logs is restricted, 31 days for a paid OMS plan. What if we have been compromised for a while and for whatever reason not detected it? Maybe it was an admin gone rogue. What if a Domain Controller hasn’t been exporting it’s logs as expected? Well, then we need to go through the logs manually. As we have a finite amount of disk space, and we could end up having to take a server offline, we will make sure that our event logs are copied off to a cloud service.
My cloud service of choice, of course, is Microsoft Azure. I have previously worked with Amazon’s S3 storage for exactly the same purpose. The first thing I have done is written a PowerShell script that will actively archive off our security logs. This script can be found in GitHub . The script has three parameters that you need to enter before you start running it, you require a storage account name, an access key and your container. The script will then upload to “folders” /DomainDNSName/Servername/ this allows you to easily identify which server from which domain the log originated.
This script relys on PowerShell 5. It’s built in to Windows 10/Server 2016. For earlier versions, you can download it from https://msdn.microsoft.com/en-us/powershell/wmf/5.1/install-configure. Note that installing this will require a reboot to work.
With this script in place, you will need to deploy it to all your Domain Controllers, along with setting up the Event Log to archive the events rather than constantly overwrite the entries. We will use Group Policy to configure the Event Log but we will then use Group Policy Preferences to place the file on the domain controllers and configure the scheduled task. Bear in mind that if you are using the policies within my repository you will have to update the path that the file is copied from to match your domain, and the path that the script will be copied to. Altering this will also mean updating the scheduled task.
To configure the Event Log by GPO, you can either edit our Custom Domain Controllers policy or add a new one. Navigate to
Computer Configuration\Policies\Administrative Templates\Windows Components\Event Log Service\SecurityConfigure the following GPO settings which are fairly self explanitory
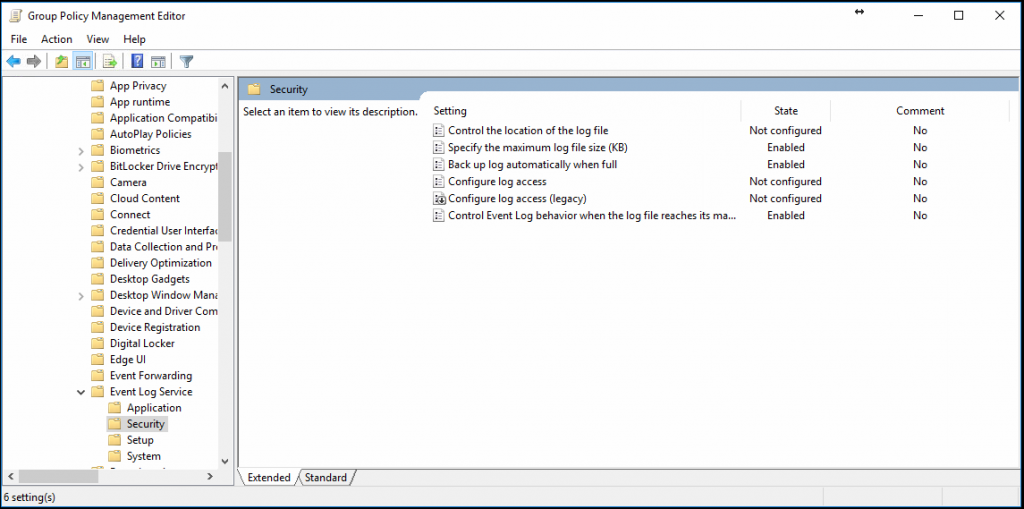
These settings will make it so that the log creates an Archive after the size specified. Use Group Policy Preferences to schedule the task and copy the file. The configuration of the task is the same as scheduling the task manually.
With these in place you should start seeing the event logs appear in your new storage account. This way, shoud anything happen you can always go back to these logs for forensic investigation.
