We all know that passwords are bad. We’ve spent years teaching users bad habits with them. One of the most prevalent attacks at the moment is credential stuffing. This is where an attacker will obtain a list of username/passwords from a breached site and replay them against other sites. The other common attack is Phishing, where a user is tricked in to entering their username/password on to a fake website. Essentially handing over these credentials to an attacker. Why do we do this? We have been taught to create a complex password. A complex password is difficult in the very nature to remember, such as 0Ge3$GV1, so once we have remembered it, we think it’s secure, I can remember it, so I will re-use it. And that’s the downfall, you use said password on a website, an attacker manages to get access to the data, decrypts your password then goes off and replays it against other sites eventually finding a match. And then your account is gone.
So, what do we do? Well, we have to ensure that each password on each site is unique. The easiest way to do this is with a Password Manager. There are plenty of free ones out there to choose from. You generate a random string to use as a password, then store it safely away. A browser plugin can automatically populate username/password combinations. But this doesn’t work as well in a corporate environment. So, what other options do we have?
Going passwordless
First of all, Windows 10 has a feature called Windows Hello/Windows Hello for Business. This has the ability to use biometrics or a PIN to sign in. You never enter your account password. Windows 10 also supports Single Sign on to Azure AD when either hybrid or cloud joined. So, first port of call is to enable Windows Hello or Windows Hello for Business. This provides a nice user experience when signing in to a workstation where they don’t need to enter anything. For machines that have a TPM but do not have a biometric device you have the option of using a PIN which is unique to that device (unless you reuse the PIN across multiple devices …. but who reuses PINs and passwords?).
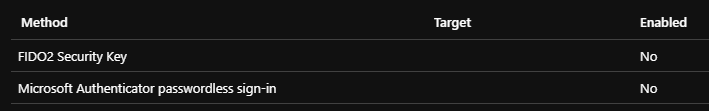
Next, within Azure Active Directory, you have the option of enabling both passwordless using a hardware key. This allows a user to sign in to Azure AD without needing a password. This is useful when they are not using their corporate Windows 10 machine. Under Security, select Authentication Methods and make sure both of these are enabled.
Something else you should already be working on is to Single Sign On everything you can. By implementing this you reduce the need for users to remember and manage passwords a multitude of passwords. You provide a good user experience accessing your applications. And, to terminate access, you only have to terminate one account. Microsoft are investing heavily in adding applications to their gallery that will support SSO with an easy configuration option.
All of this is great, but your user still gets issued with a password, what if you changed your onboarding process so that as part of the equipment handover, you configured the Authenticator App, Yubikey and/or Windows Hello for Business. Your helpdesk team have set the account up with a 25 character password that was generated using a password generator. They enter it just the once to sign the user in, then destroy the copy of the password. At this point you’re in a good place. The user cannot be phished! After all, a phishing attack only works when the user can disclose a password.
The ultimate goal and utopia would be when everything is fully automated, you onboard a user in to Workday or another HR system, this automatically provisions the user in to your chosen directory service (AD/Azure AD). From Azure AD they are then sent a one time use password that allows them to log in and set up Authenticator.
Personal Accounts
It’s well worth noting that if you have an existing Microsoft account (for Xbox etc), you can use the Authenticator App to go passwordless with this account as well. On your personal laptop, again you can use Windows Hello and as well as in your corporate world, you can go passwordless in your personal world.
Multi Factor Authentication
As well as going passwordless, the other biggest improvement to your security that you can deploy is Multi Factor Authentication. This is where as well as your username and password you will either have to enter a code from an app, SMS or Phone Call, respond to a notification in an application or use a hardware key such as Yubikey to prove your presence. Because of the second factor of authentication, even if you have re-used a password, or your password has been brute forced/phished, an attacker still cannot access without the secondary code.
It’s worth noting that phone calls and SMS are both vulnerable to ‘sim swapping’ if an attacker is determined to get access, they have been known to transfer your number to a new SIM that they control. That said, it will come down to your personal threat landscape. If you’re CIA/MI5 level, you probably want something more secure than SMS/Phone Call. 80 year old granny protecting her Facebook/Netflix account would probably suffice.
But I don’t want a work app on my personal device!
This is a common place complaint or push back. I suggest you read the following blog post. If you’re not already educating users on the benefits of MFA, educate them on how to make their personal lives more secure!
Microsoft Priorities
If you want to know how serious Microsoft is about Passwordless and Single Sign On, see the following blog post from Joy Chik, Corporate Vice President of Microsoft, Identity Division.
With these priorities, deploying Passwordless and enabling SSO for all your apps, you are well on the way towards a Zero Trust mindset. Make sure you use Conditional Access to verify every request for access, make the process slick for users but difficult for hackers. Adopting this methodology will also provide your business with a continuity and DR plan. No longer will users HAVE to be in an office, they can work from home, the coffee shop (privacy filters have been issued?) or wherever.
